 It is probable that the Post Office scandal highlights information security failings by both the Post Office and their contractor, Fujitsu, some of which I will summarise in this short blog.
It is probable that the Post Office scandal highlights information security failings by both the Post Office and their contractor, Fujitsu, some of which I will summarise in this short blog.
I, like much of the adult population of the UK, have watched, appalled and angry, as the docu-drama Mr Bates vs the Post Office has related the sorry saga of the sub-postmasters and their battle against the Post Office following the failings of the Horizon computing system. I am not going to use this blog to document the history of the scandal, which is achieved best through the excellent BBC podcast, or to vent my disgust at the behaviour of the Post Office or Fujitsu. I am also not going to consider the on-going failings of both organisations in their response to events over the past 20-or-so years.
Instead, I am going to demonstrate in this blog that I suspect that there were clear failings in the application of information security and that, perhaps, by applying ‘security by design’, this whole fiasco could have been avoided.
I am going to refer to ISO 27001 as this is an internationally recognised standard for information security and would, even without certification, provide a guide for how a responsible organisation should approach information security. It is worth noting that this document did not exist when the work on the Post Office Horizon computing system was first started in 1996. However, it’s precursor, BS7799 Code of Practice for Information Security Management, was first published in February 1995.
Basic Horizon Design
It is clear that safe engineering principles, such as ‘security by design’ have not been applied fully in the development of the Horizon system, which has been described by the Post Office as ‘imperfect and has the potential for creating errors’. Indeed, the judgement of the 2019 High Court case found that ‘In summary terms only, Legacy Horizon was not remotely robust’.
Aside from the fundamental design of the Horizon systems, complete with the apparent bugs and errors, there were wider issues in the design of this system. Segregation of duties between contractor (Fujitsu) and client (Post Office) appear to have not been applied, as well as a failure to implement Access Control and Access Rights, with unauthorised access to systems by staff enabling non-Post Office staff to make adjustments.
Logging is a fundamental part of effective information security, enabling the maintenance of an audit trail. From the apparent reluctance of both Fujitsu and the Post Office to release such information, it appears that such a log was not maintained, not retained or simply not shared when requested…which also raises a further issues around Clause 7 of ISO 27001, which requires that ‘documented information is available and suitable for use, where and when it is needed’, or even Control 8.10 which defines processes around information deletion. Oh, and of course the requirement for the ‘identification of, collection, acquisition and preservation of evidence’ relating to information security events (Control 5.28).
Furthermore, it is not clear as to what monitoring activities were in place (Control 8.16) to look for anomalous behaviour (beyond pointing fingers at the human element and not the IT systems); such monitoring activities should have identified where problems were arising.
Information Security in Supplier Relationships
It is noted that the original 1996 Horizon contract was with ICL, with Fujitsu becoming sole shareholder in 1998. However, this is no way absolves the Post Office of ensuring that they were managing the information security risks associated with using a third party (Control 5.21) and properly monitoring and reviewing the supplier information security practices and service delivery (Control 5.22). Additionally, it would be interesting to know what steps the Post Office had taken to direct, monitor and review the out-sourced development of Horizon (Control 8.30).
Incident Management
ISO 27001 is quite clear about the need to be able to implement incident management, which includes the need to be able to assess information security events and decide whether they should be classed as incidents with, therefore, an appropriate level of response. Such an approach, as well as enabling an appropriate response to an incident, would also help in the identification of trends. This, potentially, would have alerted to the Horizon issues at an earlier stage, particularly in the circumstances where more than one call was received by a sub-postmaster.
Audit
It is evident that, when deficiencies were noted, audit teams were sent in by the Post Office. However, it appears that these audits failed to address impartiality and objectivity (Clause 9), and that subsequent investigation or actions simply did not fully determine the cause of any issues or, more importantly, determine if similar issues existed or could potentially occur (Clause 10).
Management
Let’s look now at the management issues. Clause 5 of ISO 27001 specifies a number of issues around leadership and commitment, including ensuring, amongst other things, that:
- the integration of information security into the organisation’s processes;
- the resources needed for information security are available;
- the importance of information security is communicated; and
- the information security management system achieves its intended outcome.
Additionally, there are specific requirements regarding responsibility and authority, as well as reporting to senior management.
If, as has been claimed at times, senior management did not know fully what was going on, again, there were clear failings in the implementation of effective information security.
Information Security Claims
Laughably, Fujitsu claims ‘proven credentials in ISO 27001’ and want to build ‘trust in society through innovation‘, whilst their ‘security professionals constantly work to develop and extend their knowledge and expertise, taking what they have learned and applying this to improve IT security for all customers.‘ Meanwhile, the Post Office Code of Conduct claims to have ‘Information Classification standards which define how information within Post office should be classified, handled and protected’, and has links to a ‘Cyber and Information Security Policy’, as well as providing guidance for steps to take in the event of becoming aware of any information security issues or incidents. It is curious whether either organisation has actually applied their own policies and ensured that their staff have the relevant competencies and awareness.
As I mentioned earlier, ISO 27001 did not exist when Horizon was first developed, but it must be noted that the precursor, BS7799 had been published. Moreover, Fujitsu do claim ISO 27001 credentials.
Summary
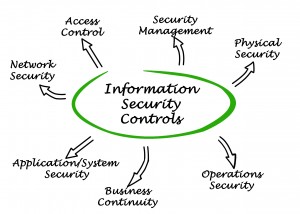
Whilst I do not have access to any of the internal documentation for either the Post Office or Fujitsu, reading through documents such as the court findings suggests that there are a number of areas where effective information security practices were not effectively implemented. A simple review of Clauses 4-10 of ISO 27001 and the related Annex A Information Security Controls highlights where it appears that there were significant information security failings. Had the Post Office and Fujitsu implemented Information Security more effectively, we have to ask ourselves whether this whole sorry scandal would or could have happened to the same extent.



